Introduction to Security in AM26x devices#
8 min read
This module will walk you through the Security basics and overview in AM26x devices.
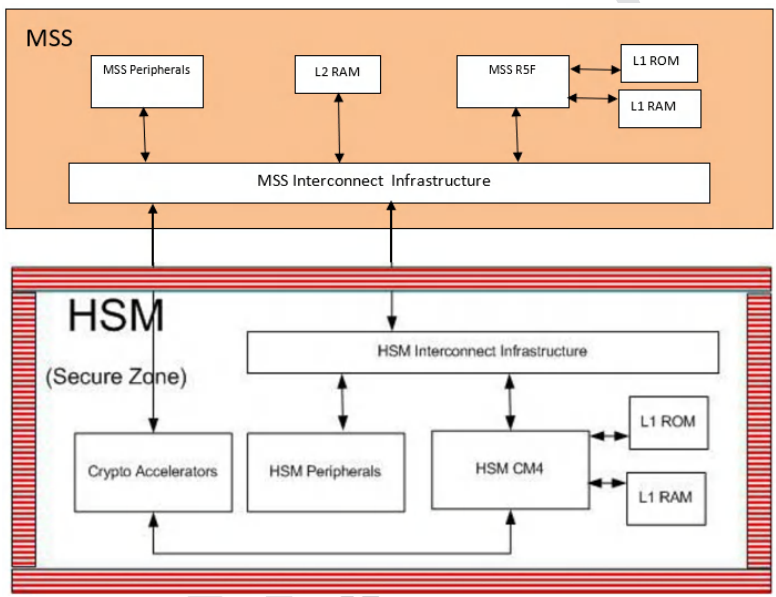
Security Architecture and HSM in AM26x#
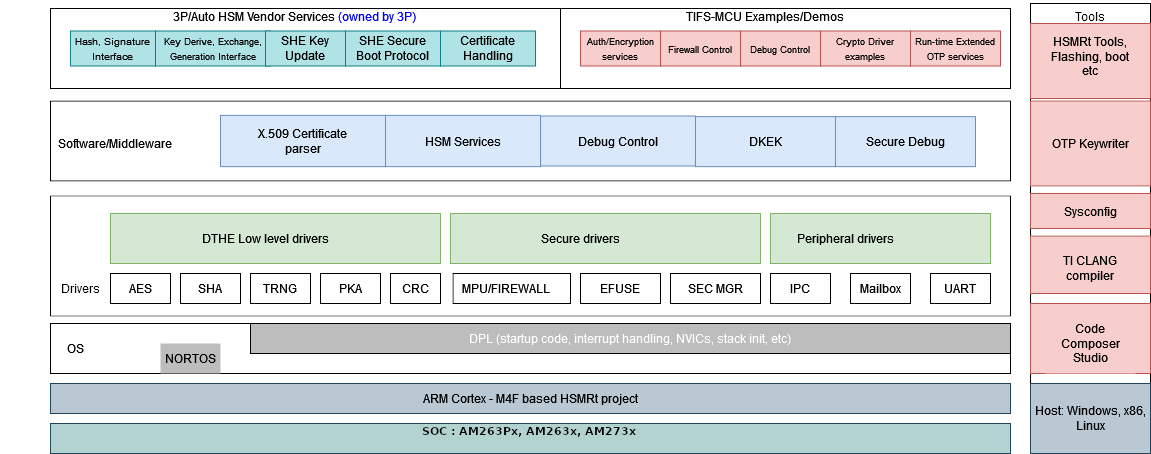
AM263x and AM263Px comes with a programmable core (ARM Cortex M4) with internal RAM (as mentioned in the table) that is provisioned in the HSM. The module host the root of trust keys, defines the secure access mechanisms, controls the debug control via firewalls and security override in case of device returns. The cryptographic algorithms can be accelerated using the HW modules provisioned within the HSM. They include acceleration of AES, SHA, Public Key Accelerator to perform big math operation for Asymmetric key crypto and True Random Number Generation. The communication with the subsystem is over a Mailbox interface and a Secure DMA is used to perform the data transfer operations to preserve the CPU cycles and provide optimized performance.
Device |
HSM RAM Size |
|---|---|
AM263x |
192KB |
AM263Px |
256KB |
List of Abbreviations#
Abbreviation |
Description |
|---|---|
AES |
Advanced Encryption Standard |
BMPK |
Backup Manufacturers Public Key |
DMA |
Direct memory access |
DRBG |
Deterministic random bit generator |
ECC |
Elliptic curve cryptography |
HMAC |
Keyed-hashing for message authentication |
HSM |
Hardware security module |
HSMRt |
HSM Run Time Firmware |
MSS |
Main subsystem |
OTP |
One Time Programmable |
PKA |
Public key cryptography |
RSA |
Rivest–Shamir–Adleman cryptosystem |
SBL |
Secondary Bootloader |
SHA |
Secure hash algorithm |
SMPK |
Secondary Manufacturers Public Key |
TIFS-MCU |
TI’s Foundational Security Firmware for TI High performance MCU Devices |
TRNG |
True Random Number Generator |
How to enable Security on AM26x devices#
Request for the package - Go to Product Page
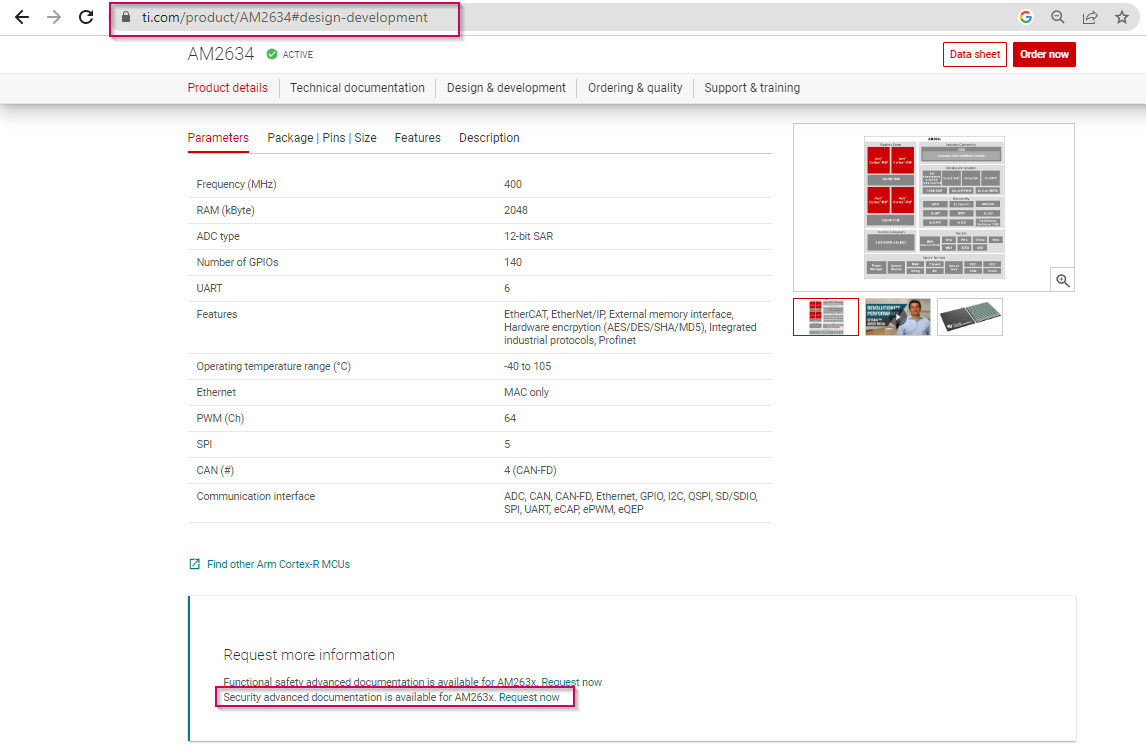
Request is granted in 3-4 business days. After the request is granted the secure packages will be available in My Secure SW.
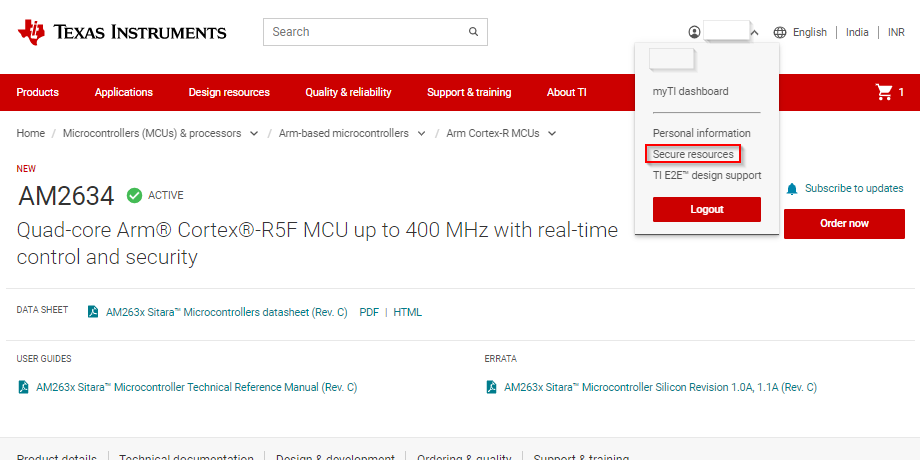
Note
This academy module contains links to MySecureSW. You must have the access to My Secure SW, so that you can access them directly.
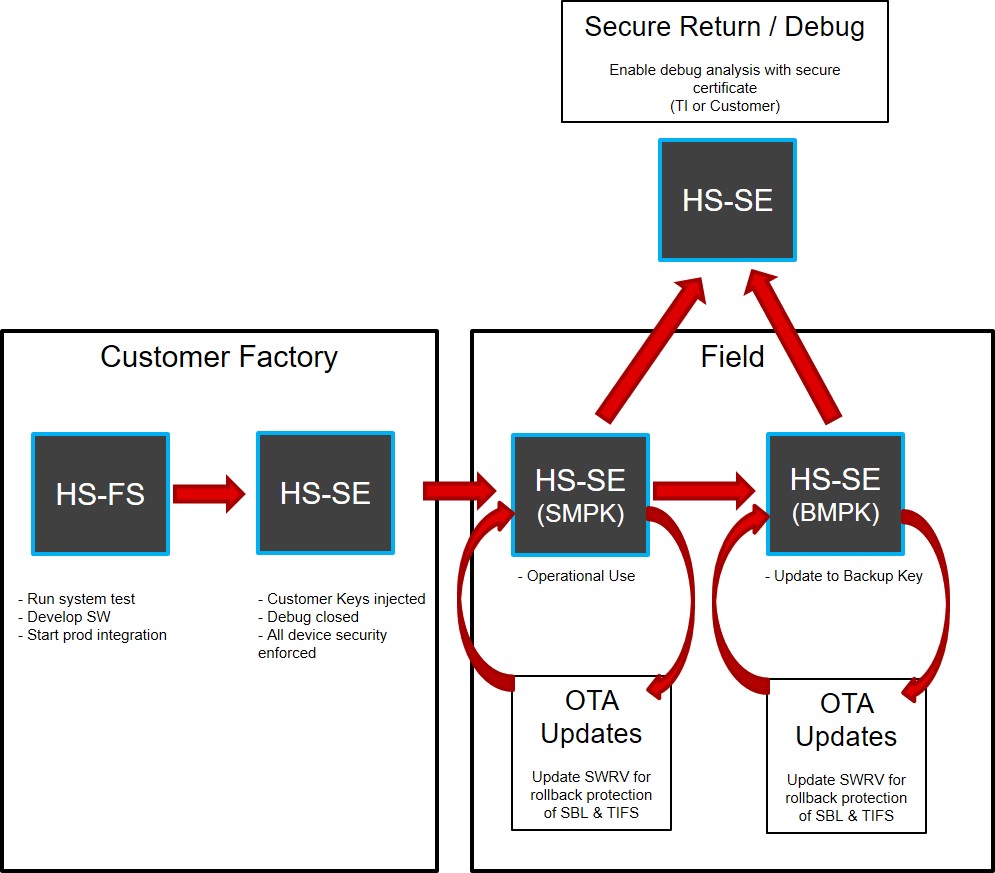
Understanding the Secure Device lifecycles in AM26x devices#
Devices are always delivered to customers in HS-FS state. The HS-FS devices are development platforms for the customers where debug ports are open for Application CPUs for ease of use during the development cycle. Customers are expected to convert the device to HS-SE devices to protect their intellectual property on TI devices from malicious attacks.
To check the lifecycle of the current device you can use the following FAQ - Link to FAQ
Device lifecycle Comparisons (HW)#
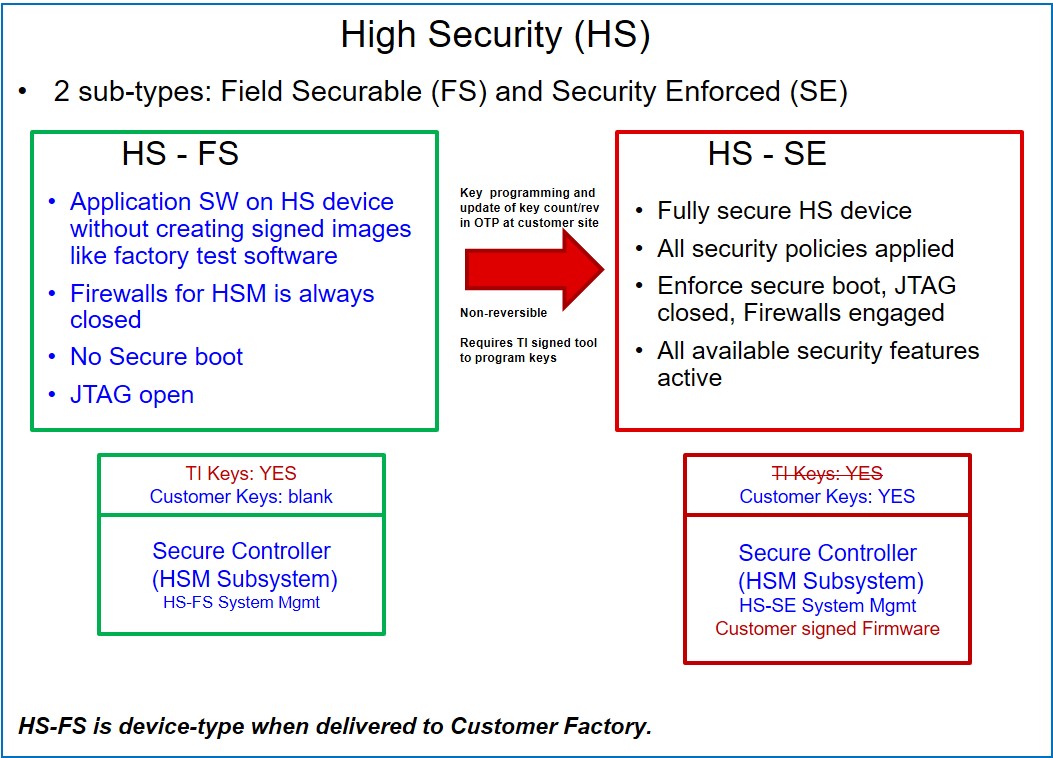
Device lifecycle Comparisons (SW)#
RBL in different secure device lifecycles#
SBL |
HS-FS |
HS-SE |
|---|---|---|
Integrity Check |
Optional |
Mandatory |
Encryption |
Not Supported |
Optional |
The integrity of SBL images depends if OID : 1.3.6.1.4.1.294.1.2 is part of the SBL Certificate. The OID stands for Image Integrity check in the certificate. The SHA512 of the image is calculated and appended in the extension information which is part of TBS of the certificate.
[ image_integrity ]
shaType = OID:2.16.840.1.101.3.4.2.3
shaValue = FORMAT:HEX,OCT:4cf4d59ef77b5d9ab28d2ceb3c9fe83cb52ae6d2
The TBS of the certificate is verified with the public key in the certificate. In case of HS-SE devices, the SHA512 of the public key is verified with the SMPKH/BMPKH in the eFuses. More details on SMPKH/BMPKH to follow.
Note
In case of HS-SE, although the Encryption is optional, it is highly recommended to encrypt the SBL.
HSM Run Time |
HS-FS |
HS-SE |
|---|---|---|
Authentication |
Mandatory (TI Keys) |
Mandatory (Customer Keys) |
Encryption |
Mandatory (TI Keys) |
Optional (Customer Keys) |
The root of trust switches from TI keys to customer keys when the device moves from HS-FS to HS-SE. More details to follow.
Note
Although the Encryption is optional, it is highly recommended to encrypt the HSM Run Time image.
HSM Run Time Firmware in HS-FS devices#
TI delivers an HSM Run Time firmware for HS-FS devices as a part of MCU_PLUS_SDK release. The firmware is called as Texas Instruments Foundational Security for TI High performance MCU+ device shortened to TIFS-MCU Firmware.
The TIFS-MCU Firmware source code is not delivered to customers nor they can change the feature for the same. The Root of Trust is maintained via TI keys and the HS-FS firmware is signed with TI keys. In case of issues while using TIFS-MCU Firmware, reach out to TI via community.
In HS-FS devices the TIFS-MCU Firmware initializes the MailBox to accept the messages from HSM Client which can be Application CPUs (R5F cores). For more information on HSM Client and features provided by TIFS-MCU Firmware - Link to HSM Client documentation
It also releases the firewalls for Crypto Accelerators so the Application CPU (R5F cores) can access the DTHE hardware via public context to do the Cryptographic offloading even in HS-FS devices. Link to Crypto Accelerators.
HSM Run Time Firmware in HS-SE devices#
TIFS-MCU serves as an add-on package on top of MCU+ SDK offering for TI High performance MCU+ devices. This can be downloaded from My Secure SW.

TIFS-MCU enables a baremetal security stack (source available) for Cortex-M4 that can be leveraged by the user to
develop device root of trust and provide foundational security services
integrate with 3P Auto-HSM stacks
The TIFS-MCU Firmware package is available for download in My Secure SW.
Conversion of Device from HS-FS to HS-SE#
TI delivers a package called OTP Key Writer which will convert the device from HS-FS to HS-SE mode. Link to OTP Key Writer.
Security Goals for AM26x devices#
Security Goal - Modules and platform protection#
Features to protect modules (hardware and software) and support platform from take-over and un-authorized modifications. Features to protect critical assets and resources from hardware and software attacks.
Modules and platform protection in AM26x devices : AM263x and AM263Px security supports secure boot that ensures that root-of-trust is established through hardware-embedded keys. This root-of-trust is used to authenticate and decrypt the boot loaders and critical software. The JTAG port is fully protected from unauthorized access.
Security Goal - Limit the attack surface for critical assets#
Isolate critical assets in protected space with heavily restricted access. Focus on protection against class-based attacks. Assume the rest of the system is compromised to protect critical assets.
Limit the attack surface for critical assets in AM26x devices : Devised HSM (Hardware Security Module), a Cortex-M4 based subsystem that is designed to operate autonomously and protect critical assets such as platform keys; acts as main control for security.
Security Goal - Sand-box security#
Security operates in an isolated environment. Data is erased after operation, prevents leakage outside of sandbox.
Sand-box security in AM26x devices : There are 2 worlds within the SoC – the secure HSM zone and non-secure world outside of HSM (within the SoC) – that co-exist, and are designed to have no leak of data outside of the HSM world.
Security Goal - Layered security#
Multi-tier approach, such that compromises do not spread and break the entire system security. Each tier operates in isolation with other tiers.
Layered security in AM26x devices : Create isolation across the processing entity, such that compromise in one entity does not make the whole system vulnerable. The HSM being a sandboxed secure zone of operation is not affected by a compromise in any other subsystem.
List of SDK links -#
Understand the bootloaders/SBL in SDK